Phishing is an act of deception.
Using misleading emails or other means of electronic communication, phishing tries to trick your victims into surrendering something of value, like money or personal information. Phishing is the practice of sending emails in which the sender pretends to be someone the recipient trusts through a device such as a laptop or a tablet. Phishing is a major cybersecurity violation no matter how you look at it.
The Difference Between Phishing and Vishing
What is a phishing attack?
Phishing is the practice of fraudulently obtaining personal information, such as credit card numbers. This was the era of America Online (AOL). Initially, crude attempts were made to obtain credit card numbers; eventually, it became comprehensive.
Phishing scams are used in many types of cybercrime, ranging from the theft of credentials to CEO fraud. Phishing attacks are designed to get an employee to click on an email link that installs a virus or other malware on their computers, giving the attacker access to the entire network of the company.
Phishing is a major component of almost all major data breaches. As an example, the Colonial Pipeline attack in 2021 was a massive ransom program in which criminals gained access by phishing a company employee.
Another prime example was the notorious Sony Pictures attack in 2014, which was followed by a series of emails sent to company executives purporting to come from Apple. The attack led to the loss of about 100 terabytes of data, including employee information and unpublished movies. The attack was funded by the intelligence service of North Korea, which ultimately claimed responsibility.
What is the process of phishing?
An example of a phishing attack would be one that tricked you into clicking on a link controlled by the attacker. Visiting a fake website by clicking on a link in one of the examples. In addition to emails, phishing attempts are sometimes sent via texts, social media messages, deceptive websites, voicemail messages, and sometimes even live phone calls. It is also possible to have a postal phishing attack that asks a victim for a web address or email address.
According to a recent study by Ironscales, you can create a phishing site that looks as real as the real thing. Researchers found that many people just aren’t paying enough attention to notice that phishing emails and websites are fake, even though there is almost always evidence that they are (see below).
What is the appearance of a phishing email?
Phishing emails typically look like this:
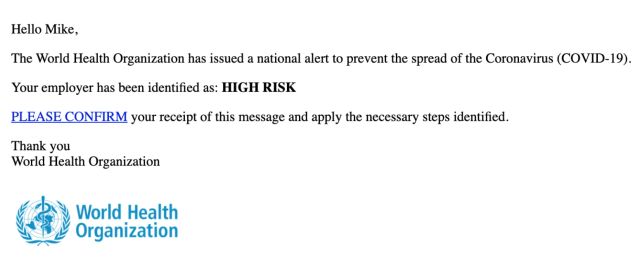
Identify phishing emails by looking for any or all of the following:
- Errors in spelling and grammar;
- Uneven logos for companies;
- You can spot malicious links by hovering your mouse pointer over them (but do not click);
- Instilling a sense of urgency or fear through the subject line;
- Free offer in the subject line or email.
- Some security companies, including Terranova and Hook Security, provide examples of phishing emails.
Phishing Attacks: How to Prevent Them
The spam filtering systems employed by some large email providers, such as Gmail, do not always work perfectly. There are some enterprise mail server applications that are more efficient, but they only work for the organization that uses them.
For the best protection, take the following steps:
Avoid clicking on suspicious links
You should never click on a link that takes you to your bank or website, requests that you change your password, or asks for any other sensitive information. Visit the actual website of the company by typing it into the address bar of your web browser, log in, and check to see if there is a genuine problem with your account. However, do not share it via email, social media, or any other electronic means. To prevent the scam, many financial institutions explicitly state that they will never ask for your password in an email.
Clicking on suspicious email attachments is not recommended
Examine the content for foreign grammar, misspelled words, odd punctuation, or ratings that seem odd. Check the links to see where they lead. Attachments should not be downloaded until the sender confirms that they have been sent.
Reusing passwords is not recommended
Password reuse across multiple websites is a leading cause of identity theft and other cybercrimes. Consider using a password manager, such as 1Password, Sticky Password, Enpass, and RoboForm, to create unique, hard-to-guess passwords for every website and service you use.
Spam filters and two-factor authentication should be used
By using two-factor authentication, you ensure that even if a cybercriminal gets your credentials, they won’t be able to access your account. Furthermore, because spam emails contain a lot of phishing content, a good spam filter will prevent you from seeing a lot of it.
Recovering from a phishing attack
Following are some steps you can take if you are a victim of phishing:
- Your computer should be scanned for viruses with antivirus software, which will detect and remove any malware.
- Any affected accounts should have their passwords changed.
- All affected accounts should enable multi-factor authentication so that no one can log in (or login again) even if they have the password.
- If you believe your account has been compromised, notify your bank or another company that has been spoofed.
- Report the phishing attack to your employer’s IT department so they can determine if the attack went beyond the network security measures.
- Consider using an ID theft protection service such as LifeLock, ID Watchdog, Zander, or PrivacyGuard, which will freeze your credit and alert you if someone appears to have stolen your identity.
If you were the victim of a successful phishing attack and it caused other damage, you may not be able to fully recover. It may not be possible to recover the stolen money if it was taken from one of your financial accounts. If you take the above steps immediately, you can minimize the damage that the hacker might cause in the future.
